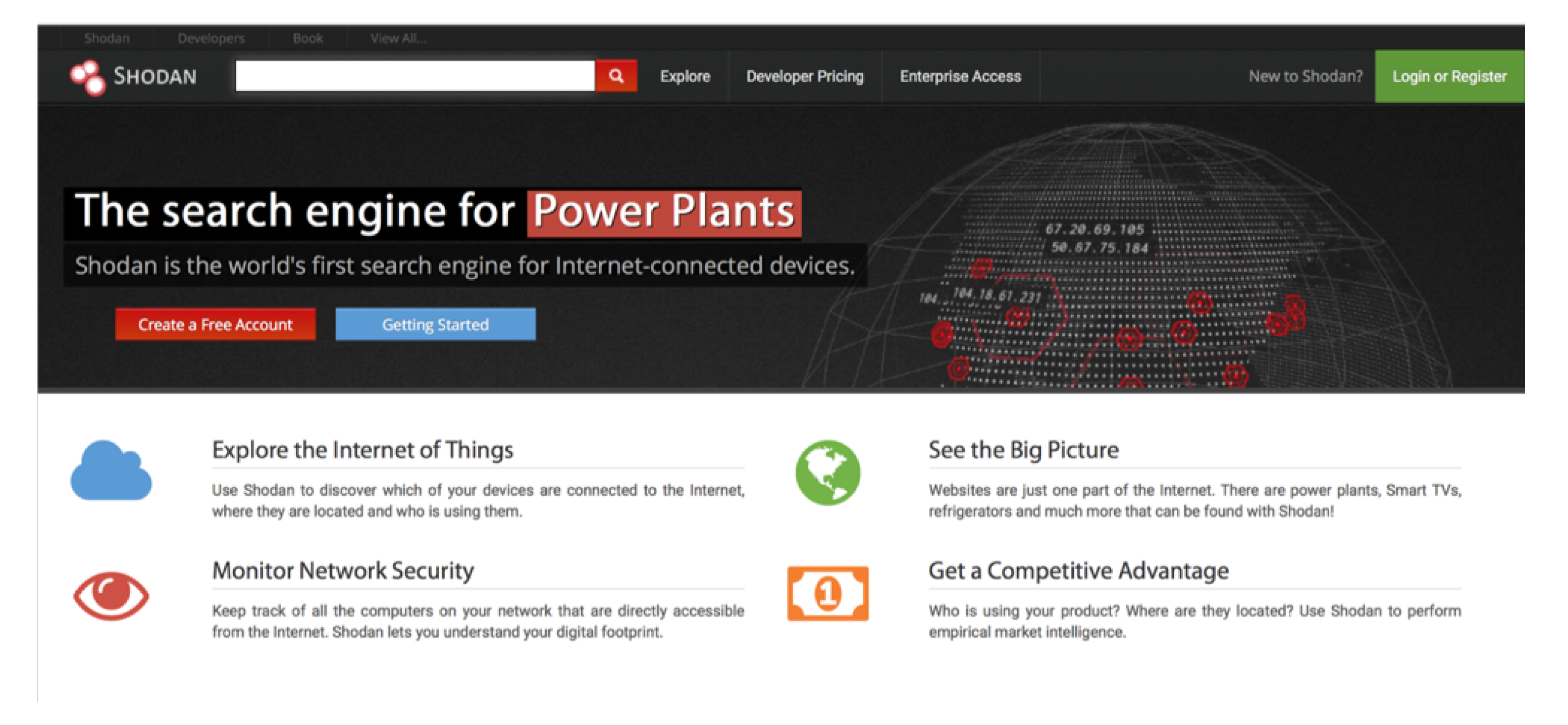
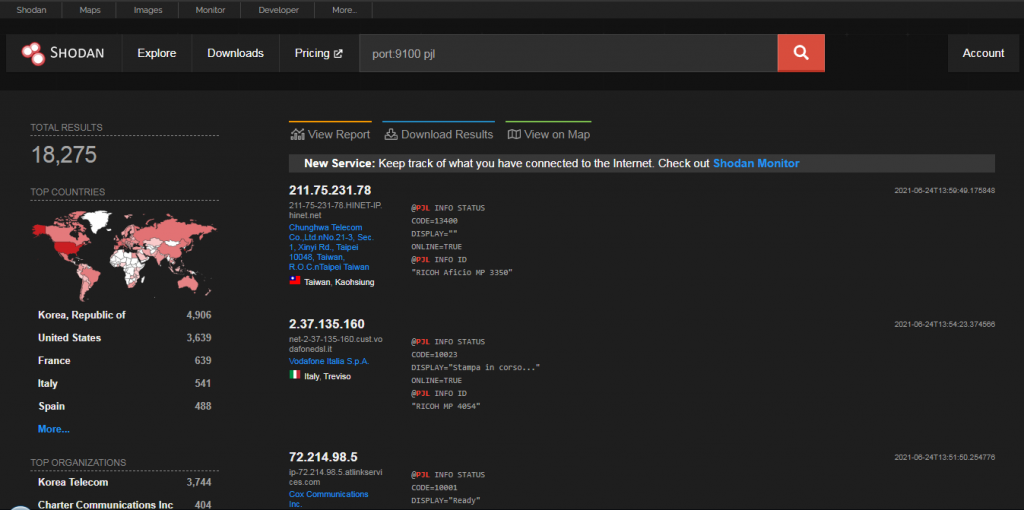
Cybersecurity Prism - What Is Shodan Exactly? You certainly know what Google is: it's a search engine that finds websites. However, it only scratches the surface of what we can find on
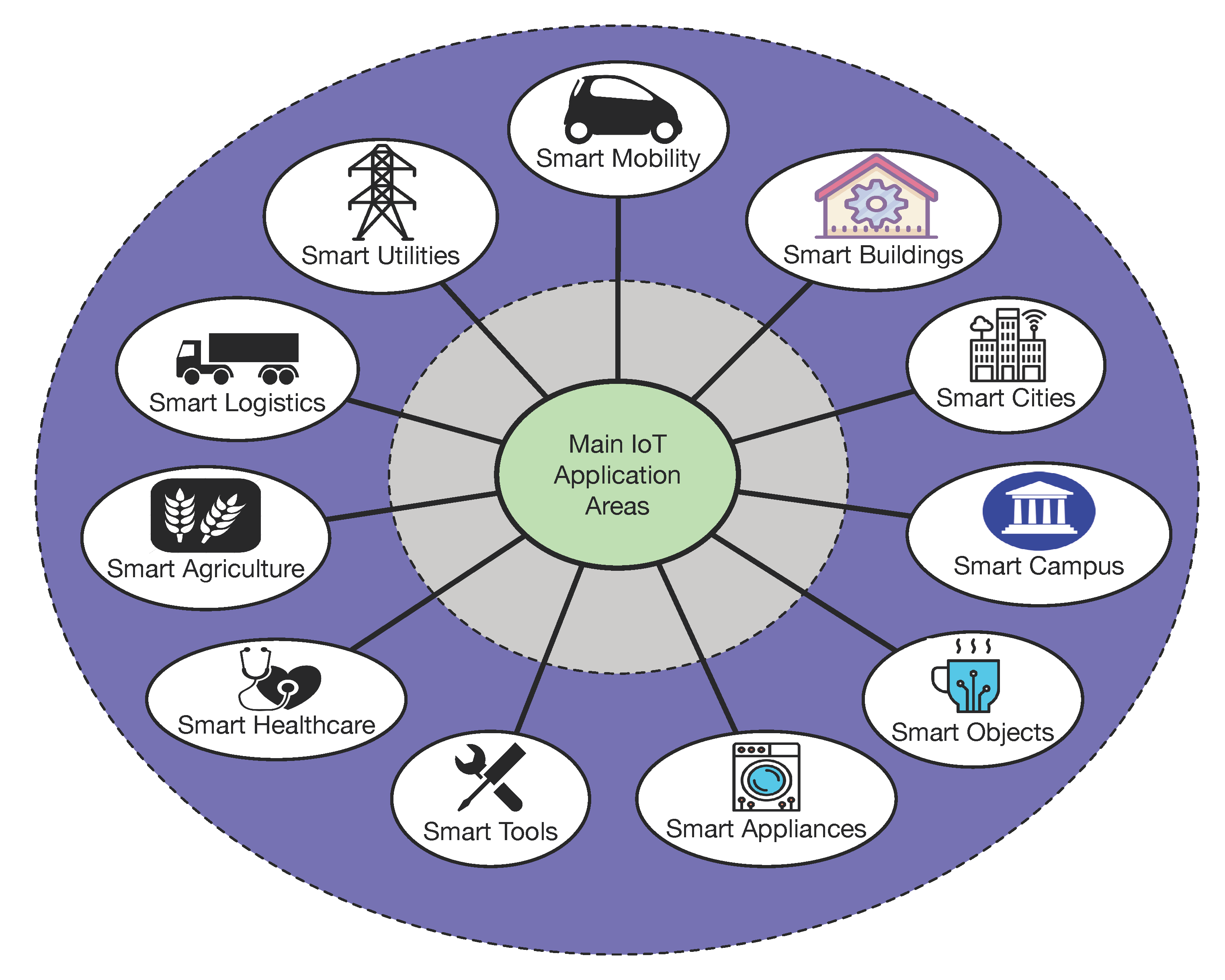
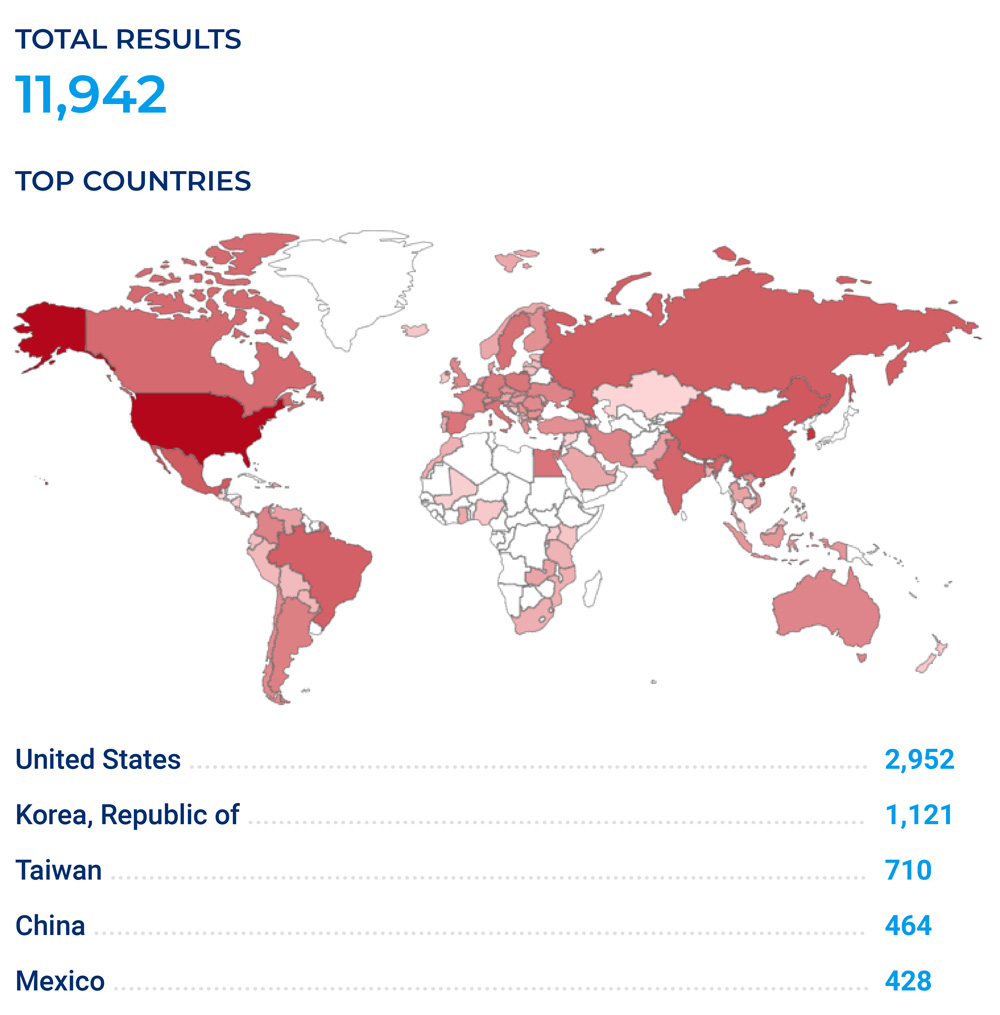
Sensors | Free Full-Text | Teaching and Learning IoT Cybersecurity and Vulnerability Assessment with Shodan through Practical Use Cases
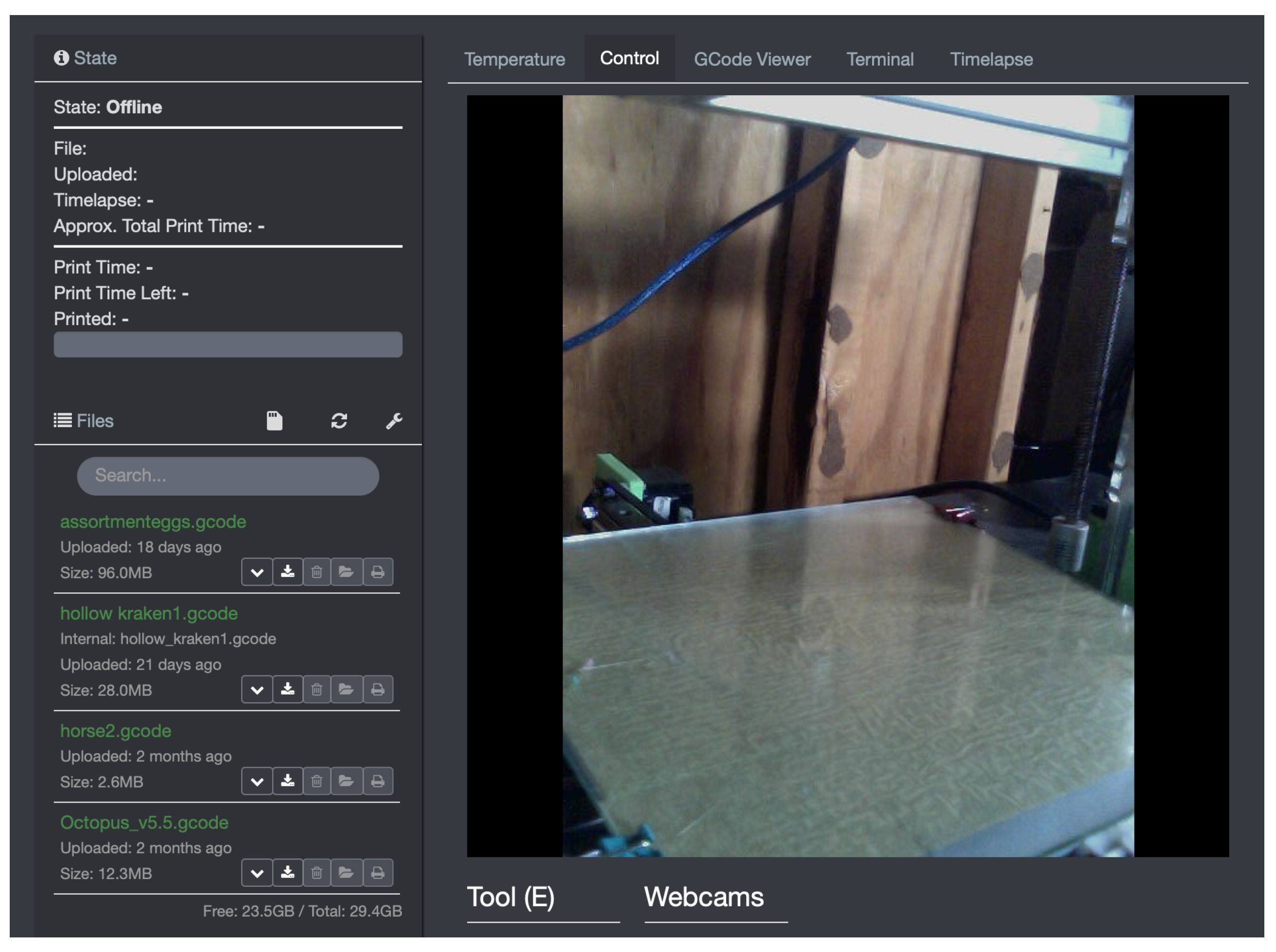
Applied Sciences | Free Full-Text | Use Case Based Blended Teaching of IIoT Cybersecurity in the Industry 4.0 Era

![Complete Guide to… by John Matherly [Leanpub PDF/iPad/Kindle] Complete Guide to… by John Matherly [Leanpub PDF/iPad/Kindle]](https://d2sofvawe08yqg.cloudfront.net/shodan/s_hero2x?1620485817)